Anthony Gioeli
Electronic Design
What's true and what's not when it comes to fingerprint sensors and multifactor authentication on mobile devices?

It seems a day can't go by without a story in the news about hacking. As more and more of our personal and business lives are transacted online, the internet has become the attack vector of choice for many criminals and other bad actors attempting to steal valuable personal information or company IP. This increase in hacking makes smartphones and PCs highly attractive targets for cybercrime. This, in turn, has led to the use of fingerprint sensors as a means to properly identify a device's legitimate user.
However, lots of misinformation swirls about the fallibility of fingerprint sensors. As a result, it's come time to examine the facts about fingerprint sensors and the erroneous belief that they can be easily hacked.
1. It's easy to spoof a fingerprint.
Not true. Despite what you see in the movies or in security demos, spoofing a fingerprint by taking a high-resolution photo or recovering a latent print is very difficult. This method is called an "attack spoof" and is logistically challenging. Very few criminals would use this method, and typically only on an extremely high-value target, not your average consumer.
One reason this #1 myth persists is that creating a spoof is easy to demonstrate if the target is a willing participant. With practice and patience, you can create a spoof of your own fingerprint by carefully creating a mold from a number of substances, such as glue and clay. But even that isn't trivial, and new anti-spoofing algorithms constantly make it more challenging.
2. Optical sensors are less secure than capacitive sensors because they store the actual fingerprint image.
Not true. A smartphone or PC that observes basic privacy and security principles never stores a complete image of your biometric information. It converts the information into a "template," where certain parameters are retained and the rest are thrown away. The template is then encrypted when the abstracted data is stored.
Since the template contains only certain details about the scanned image, but not the image itself, recreating a fingerprint from the template data isn't possible. So even if the fingerprint template is somehow extracted, decrypted and read, the data is useless for recreating the original fingerprint image. This basic principle applies to both optical and capacitive implementations.
3. If a bad guy gets the fingerprint image off of your phone or PC, he can use it to access your phone.
Not true. As stated in Myth #2, no fingerprint image will be stored in your PC or phone. Because fingerprint images aren't stored, they can't be stolen from your device.
4. Multi-factor biometric security on mobile devices is hard and/or expensive to do.
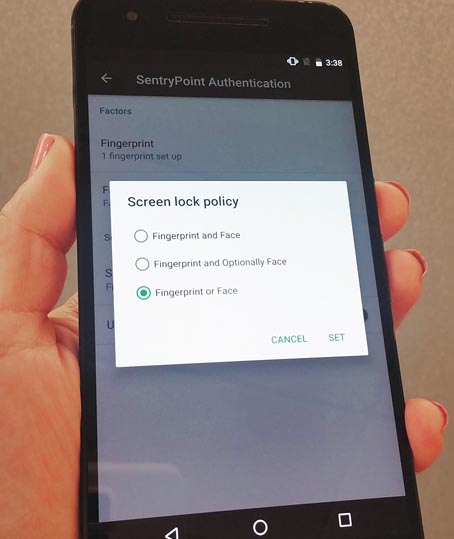
Partially true. The easy part is that many mobile devices already have fingerprint sensors and front-facing cameras, so expect to soon see the ramp up of multi-factor authentication based on your fingerprint and face (Figure 1). Other combinations, including iris and voice recognition, will likely follow.
 |
||
| Figure 1. | This smartphone features support for biometric-based multifactor authentication. |
|
The hard part is that combining multiple biometric factors into a single trust score is a complex mix of science and art, and the algorithms to do so need to be thoroughly verified. However, expect to see it become available later this year. Eventually we will see a robust ecosystem in place to support a ubiquitous, multi-factor authentication experience across different platforms and applications.
5. Contextual factors aren't enough to secure a mobile device.
True, but… it should say that contextual factors "alone" aren't enough to secure a mobile device. In combination with biometric authentication, they can be part of an overall very strong and user-friendly solution. For instance, today's smartwatches can stay unlocked until you take them off. In the future, your device will be able to use contextual factors such as location, proximity, room monitoring, etc. to stay unlocked as long as you are in your office, or to authorize transactions without additional authentication.
6. Fingerprint sensors have to be on the home button or back of the smartphone.
Not true. Fingerprint sensors are available in a broad range of form factors, including slim sensors that fit within the power button on the side of a phone. New sensors also work under the cover glass and detect fingerprints so that the physical home button can be eliminated, enabling edge-to-edge infinity displays. Looking forward, we will see solutions where the entire display can effectively scan a fingerprint from anywhere on the screen. (Note the smartphone in Figure 2 uses an under-glass fingerprint sensor).
 |
||
| Figure 2. | Multifactor authentication support can unlock a smartphone in situations where access to fingerprints isn't available. |
|
7. Biometric authentication is just for security.
Not true. Once a user's identity is established, there are myriad ways that information can be put to productive use. For example, it can be used to customize the user experience, or to select preferences. Here's a driving example: scanning fingerprint on start button sets seat, mirrors, and infotainment options to match the user (or even identify who's driving the car so that data can be used by the insurance provider/rental car provider, etc.). In a smart home, scanning your fingerprint could unlock a door, start preferred lighting and mood music settings, and restrict access to certain home features or locations (for time-shares or AirBnB rentals).
8. Optical sensors are too big/power-hungry for fingerprint scanning in a mobile device.
Not true. Technology advances have now made optical sensors small and efficient enough to be used in mobile devices, and they will be shipping in volume in the near future. Better still, some optical sensors generate a more in-depth fingerprint image, allowing for more details about a fingerprint to be used in the fingerprint template.
9. All fingerprint solutions are equal, so cost should be the deciding factor.
Not true. Fingerprint-sensor providers offer distinctly different solutions spanning different technologies (e.g., capacitive vs. optical), varying security levels, form-factor options, power consumption, durability, and notably software solutions.
It isn't just about a hardware-based fingerprint sensor. It's a two-prong solution: hardware and software working together, and both elements need to incorporate security features. Going the cheap route could expose liability to phone makers or someone in the mobile payment ecosystem down the line if proper security measures aren't implemented.
10. Biometrics are too difficult/too expensive to manage for use in enterprise environments.
Not true. Fingerprint solutions are more secure than typical username/password configurations in enterprise environments. They also eliminate cumbersome password resets and IT support calls, making them easier to maintain and support. In today's cloud-based business world, where devices can connect to corporate networks from anywhere in the world, this is critical. Furthermore, legacy PCs without a biometric solution can easily be retrofitted with one via a peripheral USB dongle-based fingerprint sensor or a mouse with embedded fingerprint sensor.
11. Encryption is enough to protect a fingerprint template file.
Not true. The purpose of encryption is to protect the template file while it's being stored, generally in a small amount of non-volatile RAM (NVRAM). However, many occasions arise when the template must be decrypted, most notably during the test for a match. It must also be protected during these operations.
A range of security architectures will tradeoff between security and cost. These solutions include:
- Match-on-host solutions:
The host processor is utilized to perform fingerprint matching,
- Secure element:
Fingerprint matching is completed on a separate integrated circuit, typically with its own secure memory.
- Match-in-sensor solutions:
The entire matching algorithm and memory is embedded in the fingerprint sensor itself. Note that a match-in-sensor architecture allows for PC environments with a secure startup process that prevents the system from booting BEFORE a confirmed fingerprint authentication is made.